“Why would anyone hack my site? There’s nothing on there.” We hear this often from our clients and new customers who come to us with some form of malicious code on their site. The truth is, you do not need to be corporate giant, storing credit card data or social security numbers on your site. Small businesses are often targeted by hackers. Hacking at this level is not personal, for the most part, it’s automated.
Why?
There is a lot of money to be made in hacking even small websites – especially in the high-volume (hundreds of sites at a time) that is typically seen. According to Jenni McKinnon at wpmudev WordPress alone has over 90,978 attacks happening per minute while Google’s Safe Browsing service blacklists up to 70,000 websites each day for malware infection or phishing scams.
WordPress alone has over 90,978 attacks happening per minute
When hackers go after WordPress sites in this volume, they run automation tools to scan sites for specific vulnerabilities. They then attack these sites en masse. Once they gain access to a series of sites, they can make money through: phishing pages, malvertising, SEO spam, drive-by-downloads.
- SEO Spam:
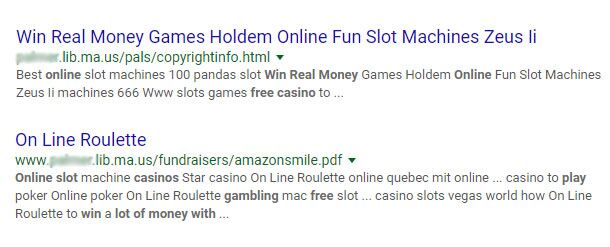
You never thought SEO could get dangerous, but hackers can use your website to artificially inflate their own Google ranking. This is one of the most frequent attack that we see on small business websites. How? One of the metrics used by Google in determining keyword ranking is the number of backlinks (other websites that link to yours) you have and the key terms used surrounding those links.
- Once compromised your site is injected with a series of back-links, your content can be overwritten, existing links rewritten, and in severe cases whole new sites and landing pages can be added to your server. The “beauty” of this is that for the most part, it all goes on behind the scenes. So this hack can go undetected until one day your own Google ranking plummets and your website is blacklisted. Or like the library in our search screenshot – you start ranking for free online casinos (or worse).
- Malicious Advertising or malvertising:
- This is pretty much what it sounds like – spreading malware through fake advertisements. So, if you are an otherwise genuine or legitimate blog or site, with otherwise genuine and legitimate advertisements, hiding malicious advertisements allows for a wider audience to view and engage with the malware. The “good” news for small companies as that these attacks typically happen at the advertising network level, so while you will be hosting malicious content, your website is not compromised in the true sense.
- Drive-by Downloads:
- This is where a visitor downloads a program without realizing it. These scams typically look like legitimate warning/alerts from your computer, but when you click on them they initiate a download and the content is typically malicious in nature.
What does this mean to me?
Well, security is a tricky thing today, and if you are thinking “Target was hacked, how am I supposed to stay secure?” you are not wrong. What you should keep in mind is that with small website hacks, most of the time they are large scale automated attacks. An organization has a list of WordPress websites using a compromised plugin and they are systematically attacked using automation tools, or sites are targeted for weak passwords. While this may not seem comforting, what it means is that reasonable safety measures can go a long way to keeping you protected.
reasonable safety measures can go a long way to keeping you protected.
- Use a unique password that is not “Password123”
- Use a unique username – stay away from obvious defaults like Admin, Test, User. Also, department titles such as Sales, Billing, Finance, last (my apologies in advance if this applies to you) don’t use your name if it’s fairly common – I’m talking to all you Mike and Johns out there.
- Use different passwords for different websites and services. If someone stole your car key they can’t also break into your home, your safe, your office, your shed, etc.
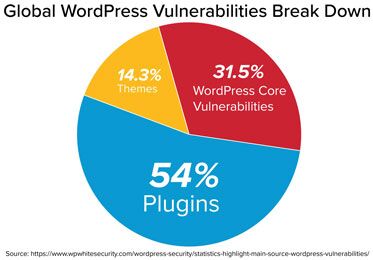
- Keep your WordPress, plugins, themes, & Php up to date. When a developer announces they have released a security patch and to update ASAP – they have also advertised to every hacker out there that all the sites using their plugin are compromised AND they have given a map to break in. A recent study by WordFence.com indicated that approximately 55.9% of all attacks are due to plugins while 16.1% are an attack on site passwords
- Don’t use abandoned plugins. If the original developer of your plugin has not made updates over the last 6 months then look into replacing it with something that’s up to date. WordPress releases a new version every 3-4 months, at the very least plugins should be making edits to be compatible with WordPress – ideally they are also making ongoing security updates.
- Invest in reasonable security measures to protect your visitors. SSL may not seem sexy, but it’s an easy way to let your visitors know you take precautions when it comes to security
- Invest in malware scanning. You may wonder why this will help, since the moment this is useful is the moment you find out everything else failed. Security scanning means that if something happens, it will be identified and resolved quickly. Rather than finding out your site was hacked because Google blacklisted you, or a customer saw an inappropriate ad; you find out the moment it happens.
But I’m already hacked
There are several steps to take next if you’ve been hacked. If you are non- technical, reach out to a service to help you clean up your site.
When looking for someone to help the key thing to ask is: will they just remove the malicious code OR will they track down how the hack happened and repair it?
This is important because if you just clean up the site then you are very likely to be hacked again. If your password has been compromised or you’re using a weak plugin, these will just be exploited again, and you’ll have to repeat the cleanup process. So be sure to find the cause of how you were hacked
be sure to find the cause of how you were hacked
The other part of the cleanup is resetting all your passwords. This is probably going to be annoying, but if someone broke into your house, you’d probably replace your locks – this is pretty much the same idea.
Next, update anything that can be updated and reinstall clean versions of your core WordPress install and plugins. There is never 100% chance of getting all the malicious code off a site without reading through every line of code. Needless to say that would be very expensive and when you’re done it would have been cheaper to rebuild. Instead we recommend replacing what can easily be replaced with clean up to date versions: WordPress, plugins, & themes.
Last, sign up for monitoring. Knowing the second something happens reduces the cost of cleanup and the impact it will have to your site. Further, if you’ve been hacked you are clearly on someone’s list of vulnerable WordPress sites and more attempts might be made.